Decryption Keys Now Available for CryptoLocker
- Published in Security
- Written by Top Speed
- Be the first to comment!
- Read: 44384 times
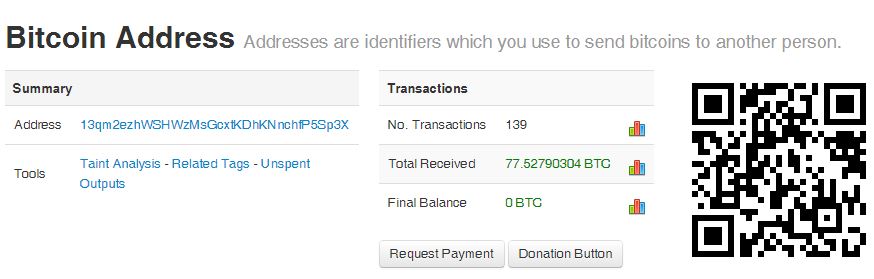
This is some of the best news the world of anti-viruses and anti-malware could have hoped for - FireEye in conjunction with Fox-IT have found and released a potential way to retrieve the private decryption key needed to decrypt files infected by CryptoLocker.  We have previously written several articles on CryptoLocker, the ransomware that began infecting computers 3rd quarter of 2013, and demanding payment of originally $300 and up to 10 Bitcoins (which hit a high of over $1200 per Bitcoin) or over $12,000 USD to be sent the decryption key. For more information on CryptoLocker see this article and this article.
We have previously written several articles on CryptoLocker, the ransomware that began infecting computers 3rd quarter of 2013, and demanding payment of originally $300 and up to 10 Bitcoins (which hit a high of over $1200 per Bitcoin) or over $12,000 USD to be sent the decryption key. For more information on CryptoLocker see this article and this article.
Until now the only way to decrypt your files was to pay the ransom and be sent the decryption key; many companies, without enterprise level backups, found themselves doing exactly that. Those who had an enterprise level backup in place had more options for restoring backups and filling in any gaps with a relatively small amount of data entry.
Recently law enforcement in association with other groups including FireEye and Fox-IT, had made major breakthroughs against the perpetrators of CryptoLocker during Operation Tovar. During the operation some of the decryption keys were discovered and those are being made available. It's not a sure fire solution for those with encrypted files, but it's a chance they didn't have before.
To find out if the decryption key someone needs is available they need to go to the website that's been setup by FireEye and Fox-IT. Once at the site you'll upload one of your encrypted files and submit it along with an email address for the decryption key to be emailed to. They will attempt to decrypt your files with one of the discovered decryption keys and if they're successful you'll receive an email with the key and instructions on how to decrypt the remainder of your encrypted files.