Great News In The Battle Against Tech Support Scams
- Published in Security
November 10, 2014 the Federal Trade Commission along with local Delray Beach Florida law enforcement raided the facilities of OMG Tech Help and Vast Tech Support; effectively closing down these and related businesses for engaging in deceptive business practices by running “a multi-million dollar computer repair scheme that exploits consumers’ fears about computer viruses, malware and other security threats.”
This is a huge win for consumers who, as the TRO Motion makes clear, have been bilked out of millions of dollars by fraudsters tricking people into paying for unnecessary tech support services or software. Included in the TRO is “an asset freeze” to allow for “equitable relief” for those victimized by this scam.
Tech support scams have been a growing industry in the past few years and we’ve written about them several times. Our advice has always been the same, take your computer or server to someone local, don’t trust the calls, emails or popups you receive.
For more information on how these scams are perpetrated read our article Tech Support Scams - Don't be a Victim.
In the case of OMG Tech Help and Vast Tech Support the scam works through a free downloadable program called PC HealthBoost (see above image); the software was developed by and is maintained by Boost Software of Massachusetts and they are included in the TRO. The software is marketed, if you can call it that, through paid for ads and popups on websites.
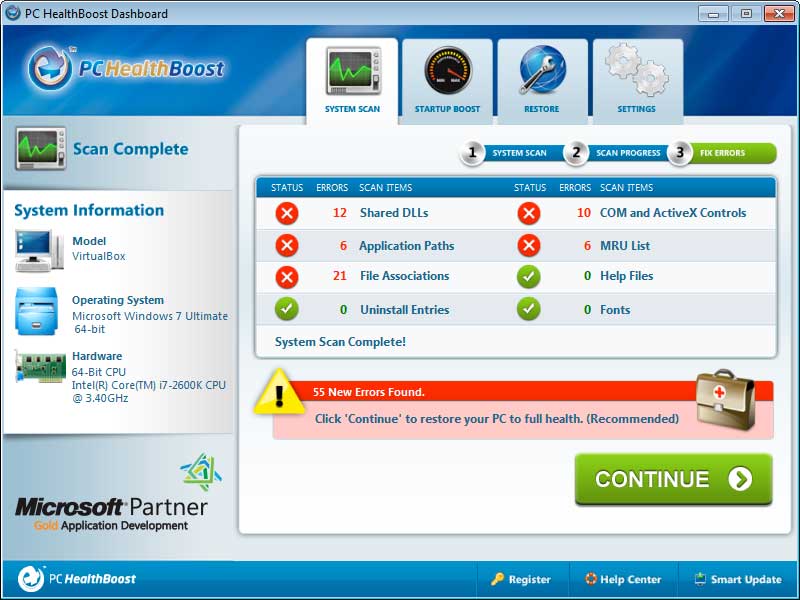 Screenshot of PC HealthBoost software scam.[/caption]
Screenshot of PC HealthBoost software scam.[/caption]
From the FTC, “Upon downloading a free version of the product, the product automatically initiates a bogus computer system scan that invariably detects hundreds or thousands of purported “errors ” in need of repair. PC HealthBoost’s bogus free scan falsely identifies innocuous and helpful files as “errors”. The Boost Defendants then offer consumers the opportunity to “fix” these errors by downloading the paid version of the software for $29.97. After duping consumers into purchasing the paid version of PC HealthBoost, the software instructs consumers to call a toll free phone number to activate the product.”
For details on some of the innocuous items identified as errors, as well as how the remote access section of the scam works see our article.
It is through the need to activate the product that the scam transitions from Boost Software to OMG Tech Help and Vast Tech Support. Now you’re in the hands of the next step of the scheme to “extract additional money from unsuspecting consumers”.
As a part of the activation the telemarketer finds a way to get you to allow them to have remote access. Once remote access was gained to the intended victims’ computers they “tricked consumers into believing that their computers are riddled with problems and in imminent danger of crashing, the telemarketers then pitch the services of technicians, including repairs and long-term maintenance programs. The Vast Defendants recommend and charge for repairs even when computers are in good working order and have no issues. Through the course of the scheme, the Boost and Vast Defendants have caused more than $22 million in consumer injury.” (emphasis added)
Vast is reported to have operated under multiple dbas including OMG Tech Help, OMG Total Protection, OMG Back Up, dowloadsoftware.com and softwaretechsupport.com.
To put that $22 million in consumer injury into perspective, consider the President of OMG Tech Help Jon-Paul Vasta’s LinkedIn Profile.
That's $22 million in not even 3 years of running this scam.
Near the end the TRO gives us another encouraging bit of information, “Before founding Vast, JP Vasta worked for Inbound Call Experts, another computer repair scheme operating out of Boca Raton subject to an FTC and State of Florida enforcement action filed simultaneously with this case.”
While it is good news that it appears a second computer repair scheme is also out of business the damage caused by Inbound Call Experts dba Advanced Tech Support, appears to be even larger than OMG Tech Help. Consumer’s reported paying $150 – $500 for each phony repair, coming to a total of nearly $100 million in revenue from consumers.
Employer review site GlassDoor.com may offers a glimpse at what Inbound Call Experts was all about. From September 2, 2014 “Former Employee…you feel like you are taking money from people who don’t have it for things they don’t need.”
The related companies in the Inbound Call Experts case are coast to coast, from Advanced Tech Support in Florida to PC Cleaner, Inc. and Netcom3, Inc. in California. The combined defendants had approximately 150 domains that they would use to lure victims in. The domains include:
- freetechsupport.com
- advancedtechsupport.com
- malwareexperts.com
- pcmri.com
- pcmriforlife.com
- superpcsupport.com
- pcvitalware.com
- fix22.com
- fixme1.com
These defendants would “partner with computer security software companies to purportedly provide technical support for particular software. In those instances, unbeknownst to the consumer the defendants pay for the phone number that appears on the software partner’s website. When consumers call the software company for assistance with a particular product, rather than reaching that software developer, they reach ICE/ATS.”
One of the downloadable programs offered specifically by PC Cleaner, Inc. which claims to show infections, but instead uses false information to trick the victim has been downloaded by users more than 450,000 times between 2011 and 2013 per the FTC filing.
This is great news for consumers everywhere! But remember these two aren't the only companies working this scam online. It’s always best to take your computer to a local trusted company!